Infolob Cloud Migration Strategy and Methodology
While cloud computing is now wholesomely accepted as the future of enterprise computing and its adoption is in full swing – every enterprise must make their own cloud strategy depending upon its requirements, budget, and future aspirations. If done correctly with a smart cloud adoption methodology – cloud benefits are multi-fold, if not done correctly – loss of money, time, and business operation hinderances are some of the common repercussions.
Moreover, enterprises are universally concerned with the question of ‘how to lift/shift, move, and improve their large data center estates to the cloud without causing much disruption to their on-going business operations and services?’. Stating the obvious, their concerns also lurk around devising the perfect migration strategy, data security, compliance, risk, costs, performance, productivity, and returns on investment.
These are indeed the paramount needs of the enterprises looking to adopt business transformation. The good news is, with Infolob’s time-tested, scientific approach to cloud adoption that is diligently embedded in our migration methodology and the Cloud Migration and Managed Services, enterprises can now easily neutralize the threats that barricade them from reaping the countless advantages of the cloud, while also instantly address all their concerns.
Note: For a free cloud assessment report before any formal engagement, please reach out us today.
Cloud Strategy with Oracle Cloud Infrastructure
As discussed, reaching the ultimate business outcomes require steeplechasing through a spectrum of cloud migration challenges. And, utilizing the marvellous Oracle Cloud Infrastructure (OCI) resources and capabilities – Infolob helps enterprises carve an elaborate, end-to-end, fail-safe, and purpose-built cloud migration strategy, precisely in line with their unique business requirements and diverse value propositions equally worth the risk, time, effort, and cost.
Oracle Cloud is the only second-generation cloud when all other providers are still selling their first-generation cloud concepts. Digital Transformation with OCI unlocks new revenue streams and operational benefits that businesses never knew existed before. With the first-of-its-kind and security-first design, and the substantial number of cloud regions, OCI addresses data protection, sovereignty, and regulatory compliance issues much more strongly than any other cloud provider.
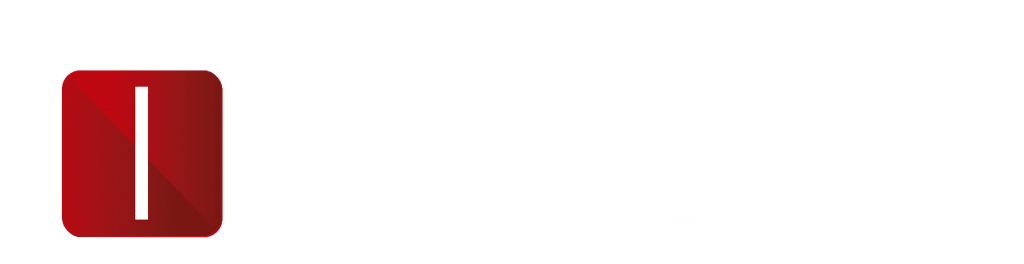
In the following, Infolob demonstrates what is inside an ideal migration process, covering all the stakes, complexity, and effort involved in the road to transformation. We break down an ideal cloud migration strategy into following four phases –
Define, Design, Deliver, and Operate
The significance of the quadrant develops from the fact that, at the core, it is a fully outcome-based iterative approach, with a versatile framework that fits all types of digital transformation initiatives — across technologies, as well as large-scale data center migrations.
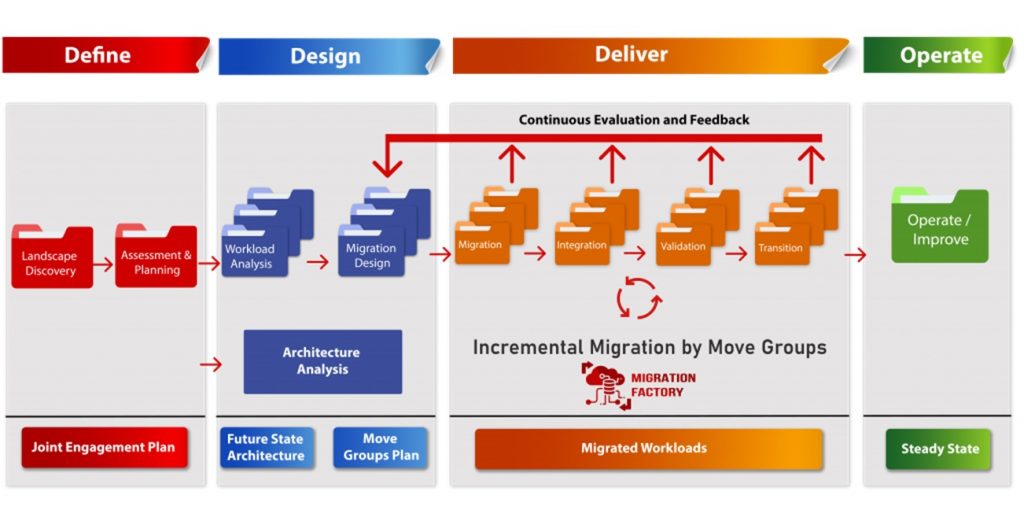
Define
Under the define phase, outcomes like the scope value hypothesis, migration effort estimation, Joint Engagement Plan, and resource commitment for Design phase are achieved via customer profile, landscape discovery, value storyline, cloud visioning, potential hypothesis, and effort estimation.
On the ground, the Define phase is predominantly about assessing the infrastructure requirements, middleware and database requirements, the current state of applications, dependencies, interfaces, configurations, integrations, SLAs, environments, followed by perusing the application specific requirements (infrastructure, middleware, etc.), testing, target platform, etc.
However, the features that make Define phase the foundation of a robust migration strategy are the principles of migration, and the ‘7R’ models of cloud migration along with the value-effort scale.
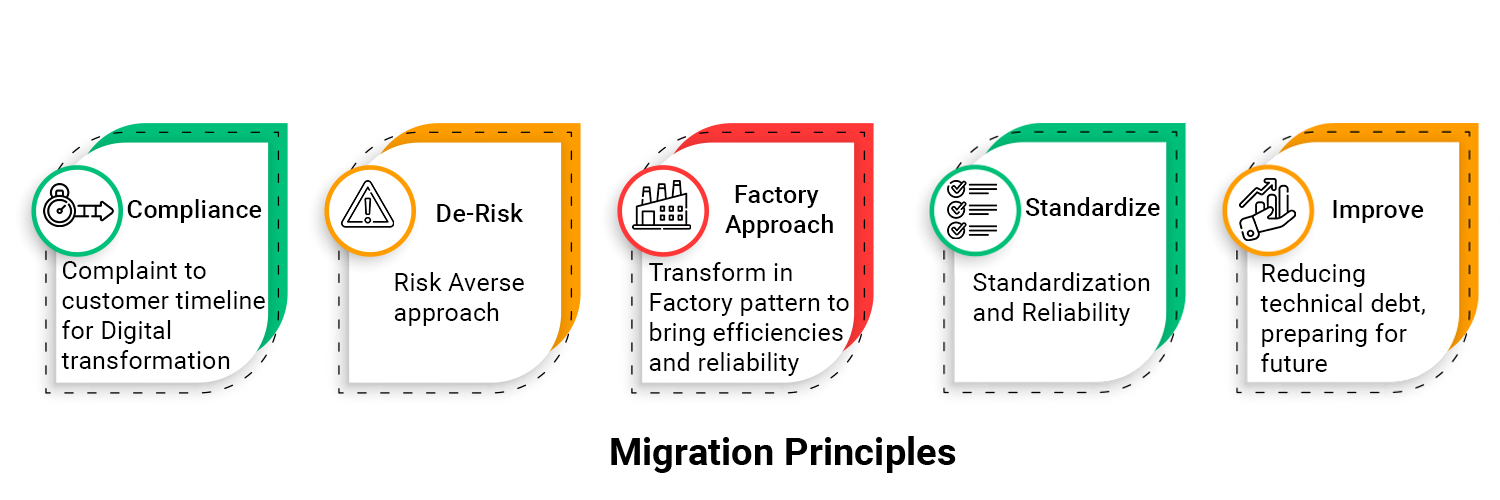
1.1 Principles of Cloud Migration
For addressing the unique customer requirements, abiding by the criticality of timelines, minimizing risks, and standardizing and improving the overall process –the principles of cloud migration come into play. As discussed in the following section, these principles chiefly encompass compliance, risk, and standardization to ensure a factory-based approach in delivering cloud migration to enterprises within the required timeframes, while also addressing the potential risks during migration, and resulting in standardization of the target landscape and higher reliability of services through automation.
Compliance: It simply refers to high-stakes nature of cloud migration, requiring the modernization process to comply with a set timeframe, or perhaps, the recovery time objective (RTO). Ensuring compliance, therefore, is about ensuring that each segment of the process is always within the specific deadline.
Security: Organizations look for assurances that their information is appropriately safeguarded and that the information security policies, standards, and requirements are being met. The basic objectives for protecting information are described in the classic, and easily understood as “CIA Triad”: Confidentiality, Integrity, and Availability.
De-Risk: Before setting out to choose a cloud migration strategy, enterprises must eliminate as many risks from the transformation process as possible. We call it the risk averse approach. One good example of de-risking cloud migration can be the data center exiting strategy that leverages an ‘application-by-application’ approach, as opposed to a complete exit, allowing for appropriate prioritization of funding and resources while infusing stability to the entire migration process.
Factory Approach: This principle in cloud migration is about moving workloads in the most efficient, reliable, and conspicuous manner possible, which is only achievable by blending tools, processes, people.
Standardize: The principle of standardizing is abiding by the accepted standards in service, resource, and network management, or simply outperforming them. Standardization is helpful everywhere, especially, where high technicality and high stakes are involved such as in cloud migration.
Improve: Improving is all about paving the way for future, and broader revenue streams by reducing technical debt. This simply means that measures taken in forming a cloud migration strategy should not be short-sighted. Businesses must look for the big picture and save the expenses often incurred in short-term choices.
In a nutshell, all these principles are the foundational for any cloud migration strategy to successfully form and execute, and hence, shall always be used as a guide.
1.2. The ‘7R’ Model of Transformation
The ‘7R’ model of transformation by Gartner is the key to architecting and communicating an enterprise’s application transformation roadmap. It simply enables formulating concrete and most relevant decisioning, encircling each application’s due transmission in the cloud. For both operational relations, and simplification, we recognize these models under Transform, Optimize, and Manage category, as shown in the figures below. However, let us also discuss each one separately: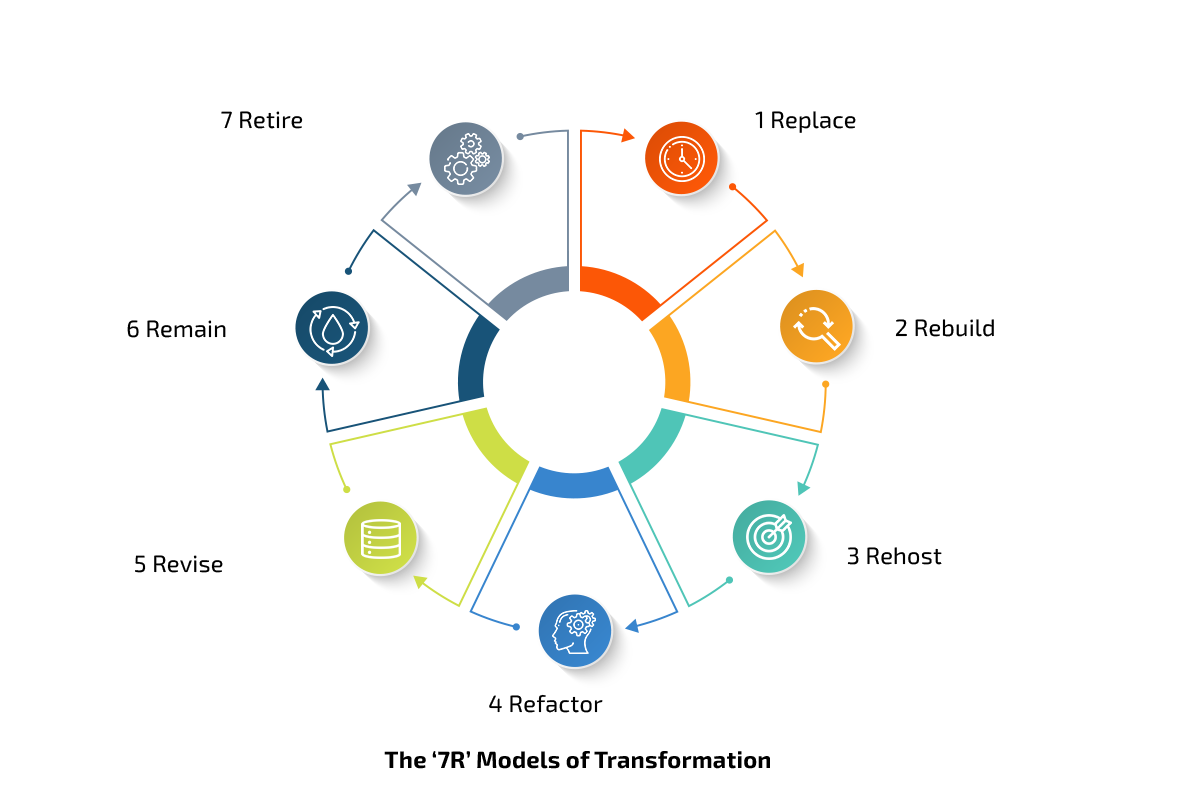
1.2.1 Replace
Beginning from the highest value/effort towards the least, the first ‘R’ is for ‘Replacing’ aging applications with cloud-based, SaaS services including Human Capital Management (HCM), Enterprise Resource Planning (ERP), Supply Chain Management (SCM), Customer Experience (CX), and so forth. Oracle has a complete, widely adopted set of such applications, including the Oracle Cloud Fusion SCM, or the Oracle E-Business Suite further encompassing 90+ modern applications — each revolutionizing a specific sphere of management, while also affording businesses the perks like real-time business intelligence, asset monetization, IoT, etc.
For example, the Oracle Fusion Cloud Inventory Management is enabling manufacturers to obtain real-time visibility across all distribution hubs for high fill rates, proactively deal with the fluctuating demands, or simply using the PAR-feature (abbr. for planned automated replenishment) for restocking critical items, on top of the unparalleled analytical capabilities, all while cutting costs.
However, one downside or the high-effort task for enterprises adopting ‘Replace’ is they must not only make tweaks to the cloud-native applications, but they also rethink and reengineer the business operations, for instance, the value chain. Hence, it is not advisable only for enterprises with applications with a quite unique set of tasks, for example, the Customer Relationship Management (CRM). For the rest, SaaS is a wonderful opportunity. It is not a surprise that, according to a data scientist published on Forbes, the SaaS revenue alone is expected to exceed $233 billion by 2022.
1.2.2. Rebuild
The next ‘R’ stands for ‘Rebuilding’ the legacy applications that, for the most obvious reasons, are incompatible with the public cloud infrastructure. And, although they have till now performed their duties most sophisticatedly, these applications were developed when the modern-day cloud environment was not in the picture offering new and infinite business value, and competitive advantage. Besides, the other ‘Rs’ like ‘Refactoring’ or ‘Rehosting’ (coming up next) would not be feasible options in such cases either. Hence, ‘Rebuilding’, that involves rewriting from scratch towards an advanced cloud-native architecture is the way to go.
Advantages of rebuilding applications
- Increased flexibility, and strategic agility: A modern, logically-crafted, scalable, fully cloud-native application can generate enormous long-term ROI, while unlocking the avenues for added strategic agility in adopting more futuristic technology.
- The marvels of cloud: As a result of a complete rewriting and rebuilding, applications inherit the entire spectrum of advantages offered by the modern cloud, including scalability, performance, resilience, availability, cost-efficiency, and so forth.
- Security: A cloud environment, especially if it is the Oracle Gen2 Cloud, delivers exceedingly smart, and robust security. For instance, with the Oracle Cloud Guard and Data Safe, security is becoming the reason enterprises rebuilding their applications on the Oracle Cloud.
The shortcomings of ‘Rebuilding’
Like in any other transformation option, ‘Rebuilding’ needs leapfrogging the prolonged processes and heavy resources requirements, including more application asset size – CPU, storage, memory; dependencies – network traffic, etc. This shall naturally increase the cost, nevertheless, multiplying revenue streams that often follow such business investments. Temporary complexity in DevOps is yet another shortcoming the ‘Rebuilding’ option entails.
1.2.3. Rehost
Rehosting, a.k.a., ‘lift and shift’ is one of the most attractive transformation options. In which, applications and associated assets are directly moved to the cloud—using the ready-made tools often available for virtual-to-virtual migration—essentially for accessing the conveniences of the modern cloud architecture. ‘Rehosting’ also offers minimal alterations in the code/application itself. This means a rehosted application can run the same OS, same version of application, and database software under the same topology.
What are all the advantages of ‘Rehosting’
- Low-cost: Leveraging a general ‘rehosting’ cloud migration strategy must be a cost-effective one, simply because it dodges any significant development or ‘tailoring’.
- Zero variation in code: All the applications are directly rehosted to the cloud, without going about any major alteration in code, and thereby, disarming the development and testing expenses that typically entail such changes.
- Clean, untouched architecture: Upon a successful migration to a second-generation cloud architecture like the Oracle Cloud, absolutely zero changes are required in most cases – to the surrounding infrastructure, or business operations. To put it differently, both monitoring ports and event management continue unaltered.
- Elastic engagement model: ‘Rehosting’ helps all the sceptic enterprises to move partially to the cloud. Hence, giving them the opportunity to ‘test-drive’ the vendor, the environment, etc., without having them to commit large-scale migration efforts at once.
- The unending list of cloud-native capabilities: ‘Rehosting’ allows for a fresh start with cloud-native applications, while also reaping the implicit benefits like the auto-provisioning, fully-managed data processing and storage services, microservices, infrastructure as a code (IaaC), pay-as-you-go payment model, and so on.
The downsides of ‘Rehosting’
Although popular, ‘Rehosting’ is often rebuffed by most businesses, especially in a time when personalization is seen as the projections of success. Let us see what else are the downsides of rehosting in cloud migration.
- Rigidity: Business adopting the popular cloud components under the ‘Rehosting’ option often cautioned against making aggressive changes in the application applications, as doing so may jeopardize the stability and performance while voiding the SLAs.
- Application requirements: Experts must pay keen attention to mapping application requirements in the cloud configuration during migration. Inability to do so can result in a disaster.
- Hindrance in performance and network latency: The shortest path to cloud migration often translates to zero optimization of the applications toward the new infrastructure / environment, often resulting in unsatisfactory performance and high latency problems. Moreover, despite the numerous advantages of the conventional cloud, some opportunities remain untapped, e.g., governance, security, etc.
1.2.4. Refactor (Re-platform)
The ‘R’ of ‘Refactor’ is all about shifting of applications to cloud without any modification to their functionality, however, with technology optimized for the target platform. This involves upgrading of OS using platform images, upgrading applications, database software, and the utilization of cloud platform services. Further, a concrete migration strategy like ‘Refactoring’ requires for consideration of the portability of the existing code base and open development abilities before everything else. Plus, reinstallation on target is always required, as in physical to virtual.
The value propositions of ‘Refactoring’
- One vs. many: In ‘Rehosting’, enterprises move only a single on-prem server to a cloud-based virtual machine (VM), while in ‘Refactoring’, they reap the option to move to multiple lightweight VMs, thereby, making the process of scaling-out and back like a piece of cake. This also efficiently minimizes resource expenditure and translates into long-term ROI.
- Unlocked durability of the Oracle cloud: Once the applications are decoupled and reassembled with the managed services, they instantly assume the durability and resilience of the Gen2 cloud infrastructure.
- Simplicity: It is because the upgraded, and simplified cloud-native applications along with the microservices architectures can help enterprises achieve higher operational efficiency while seamlessly meet new customer needs.
The downsides of ‘Refactor’
Prolonged process: Enterprises should keep in mind the resource-intensive factor of the ‘Refactor’ migration strategy, on top of the added complexities involved. Especially, as compared to ‘Rehosting’, it takes a longer span of time to begin manifesting real value for the businesses. But then, Rome was also not built in a day.
High risks: This migration strategy is among the most elaborate options, and it does involve a great deal of skill and experience in DevOps, code, automation, and more. If not implemented correctly, ‘Refactoring’ can lead to unwarranted errors in the configuration/infrastructure, which shall further result in more costs, downtime, and finally affecting your business.
1.2.5. Revise
The ‘Revise’ strategy is suited to enterprises looking to move applications to cloud for supplementing its functionality with new, innovative, cloud-native capabilities including the cloud integration services, extending the applications with low code, cloud-based development, or adding cloud analytics, etc. ‘Revise’ is also essentially revisiting the on-prem applications, adding them with the up-to-the-minute advancements rolled-out by the Oracle Cloud. Hence, in a nutshell, with ‘Revise’ strategy, your applications’ functionality stands greatly enhanced, given significant changes in the legacy enterprise applications, and PaaS is undertaken.
1.2.6. Remain
‘Remain’ is for enterprises who are required to stall migrating to cloud at this moment, as there may be some information they are still awaiting, or they must delay because of various factors, for instance, it is simply not viable for some legacy applications to be shifted to the cloud for considerations associated to latency requirements or compliance. And, sometimes, enterprises opt for ‘Remain’ simply because the value propositions projected from migration fail to outweigh the investment of cost and effort required. To those enterprises, it is advised that they keep track of the change in landscape (technical, or of compliance) and set out to plan modernizing as soon as they have the opportunity.
1.2.7. Retire
‘Retire’ is for decommissioning of the applications out of obsolescence. This strategy is for applications that have outdated to a level that they are incapable of any further upgrading, or perhaps the application’s usability is no more required. It is often seen among enterprises recently undergone acquisitions/mergers. In such a case, enterprises should take it as an opportunity to re-check their aging application portfolio and go for a mix of ‘Retire’ with another strategy in the list.
A Quick Rundown on the Define Phase
- Infrastructure Assessment: This part of the Define phase consists of comprehensive information gathering, validation, and various assessments on the infrastructure relating to its existing setups, and its new requirements including the individual needs of the middleware and database.
- Application Assessment: The other segment of the Define phase is information gathering and validation on the applications, followed by defining of the application infrastructure and middleware demands, their current state of dependencies, interfaces, and configuration. This part also features the discovery of various application-specific requirements that can range across databases, file systems, shared data, latency, and more. The defining of the testing environment requirements, target platform, etc., are also attributable to the phase.
-
Design
This phase is reserved for determining a business’ current position on its operations, the level of technology, infrastructure it has access to, the existing constraints, architecture principles, future state ambitions, etc., for sharply aligning the cloud migration design with the organization’s strategic goals.
Note: The results of the Design phase are based on multiple workshops, and deep discovery transcending across the business, technology, applications, and workloads, accompanied by a three-dimensional analysis for arriving at the Future Application Landscape (FAL), Future State Architecture (FSA), and Move Groups plan.
* Move group is a logical unit of applications that are treated in conjunction to each other for better management, in terms of planning, execution, and reporting, discussed in the coming sections.
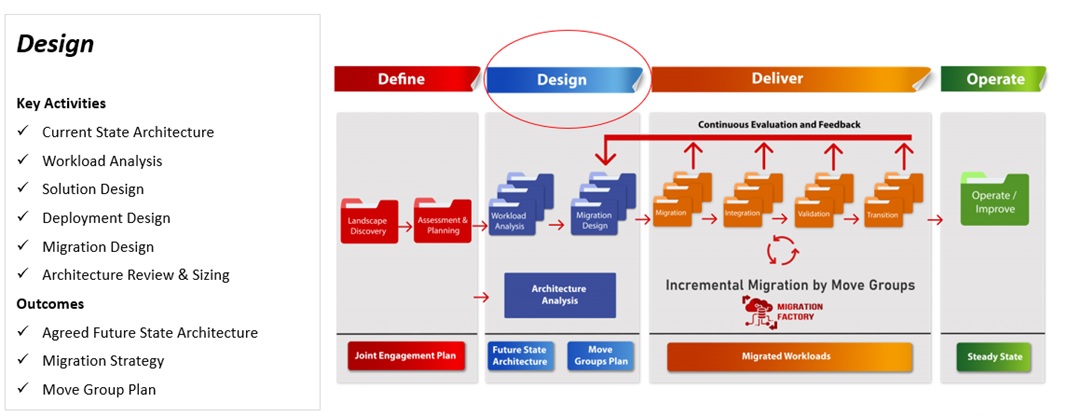
The Elements of the Phase Design
The framework for Design phase can be divided into Technical and Functional assessments. From the assessment of the application stack, databases, licenses, regulatory compliance, security, storage, servers, 3rd-party appliances, and networking to applications profiling, complexities, business criticality, deployment environment type, disaster recovery, and application dependency are thoroughly conducted.
In particular, the application profile allows for a systematic discovery and assortment of each business-critical, and non-critical application, test and development environments, and proof-of-concept (POC) migrations, resulting in migration plan, patterns, and efforts on top of Future Platform Architecture, and FAL.
2.1. Move Groups
In the large data center estates, or perhaps any on-prem infrastructure, the phase – Design plays a critical role in identifying the relationship between the applications, and the low hanging groups, also known as the Application dependency mapping. It is a complex process of figuring out which applications are dependent on what, in the context of the entire network infrastructure. Needless to mention, Application discovery along with dependency mapping are the key to Move Groups Classification, and thereby, a successful migration project.
Move Groups, therefore, are logical units of applications treated together for better management in terms of planning, execution, and reporting. The key to delivering a large-scale transformation is to break the work into smaller manageable chunks so that utmost efficiency, less risk, and less dependency upon business users is guaranteed.
Moreover, they are the bundles of related apps, driven by bounded contexts, where ‘related’ is informed by:
- analysis from business and technical points of view
- participation in a common business process
- belonging to a similar business context
- having dependencies, such as client relationships, heavy co-integration, latency requirements, etc.
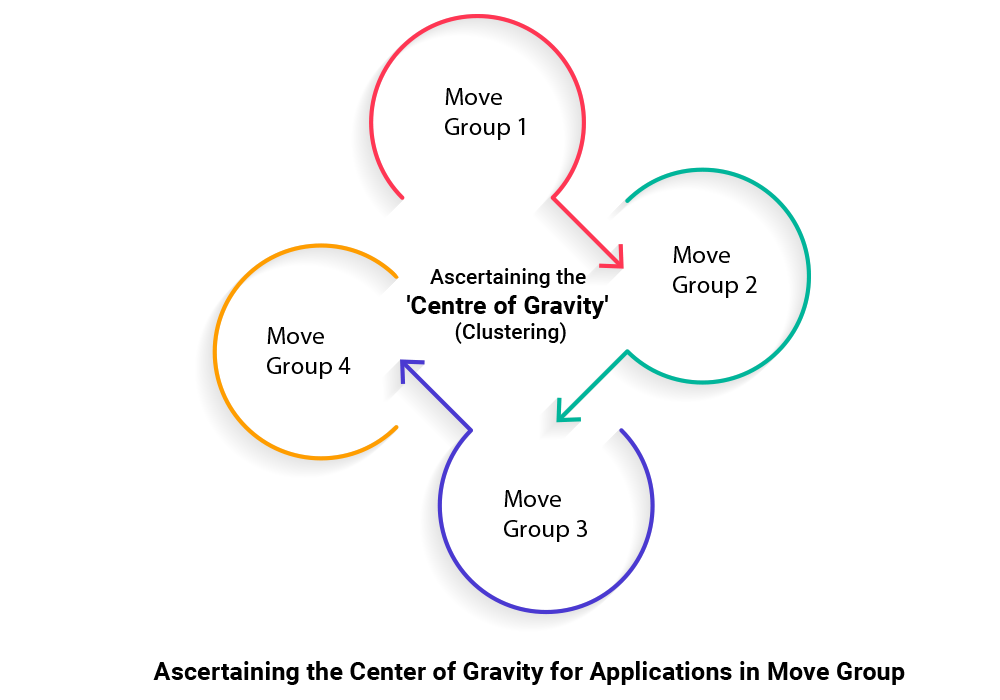
To ensure the success of the transformation, within the move groups, the solution considers testing effectiveness of migration/remediation patterns within the group by applying them for a smaller subset of applications within the move group. This helps in fine-tuning any of the solution elements and applying the learnings to the subsequent applications. Also, for structuring and de-risking the overall migration, move groups are always leveraged to migrate the subsets of the total estate as the logically coherent, application groupings. Hence, the role of Move Groups is beyond essential in strategically undertaking cloud migration. Having said that, Move Groups also depend on the 3-dimensional analysis to add further logic into the operation.
2.2. The 3-Dimensional Analysis
The 3-Dimensional (or, three-dimensional) Analysis extracts inputs from Business Assessment, Application, and Technology Assessment in multiple iterations – ranging across operations, platform, people, security, application profiling, business criticality, deployment environment type, software versions, integration, topology, CI/CD, DevSecOps, etc., and hence, is a scientific and time-tested approach to ensure the Move Groups decisions are effective to the brim. Hence, in other words, the 3-dimensional analysis is the extension of Move Groups approach.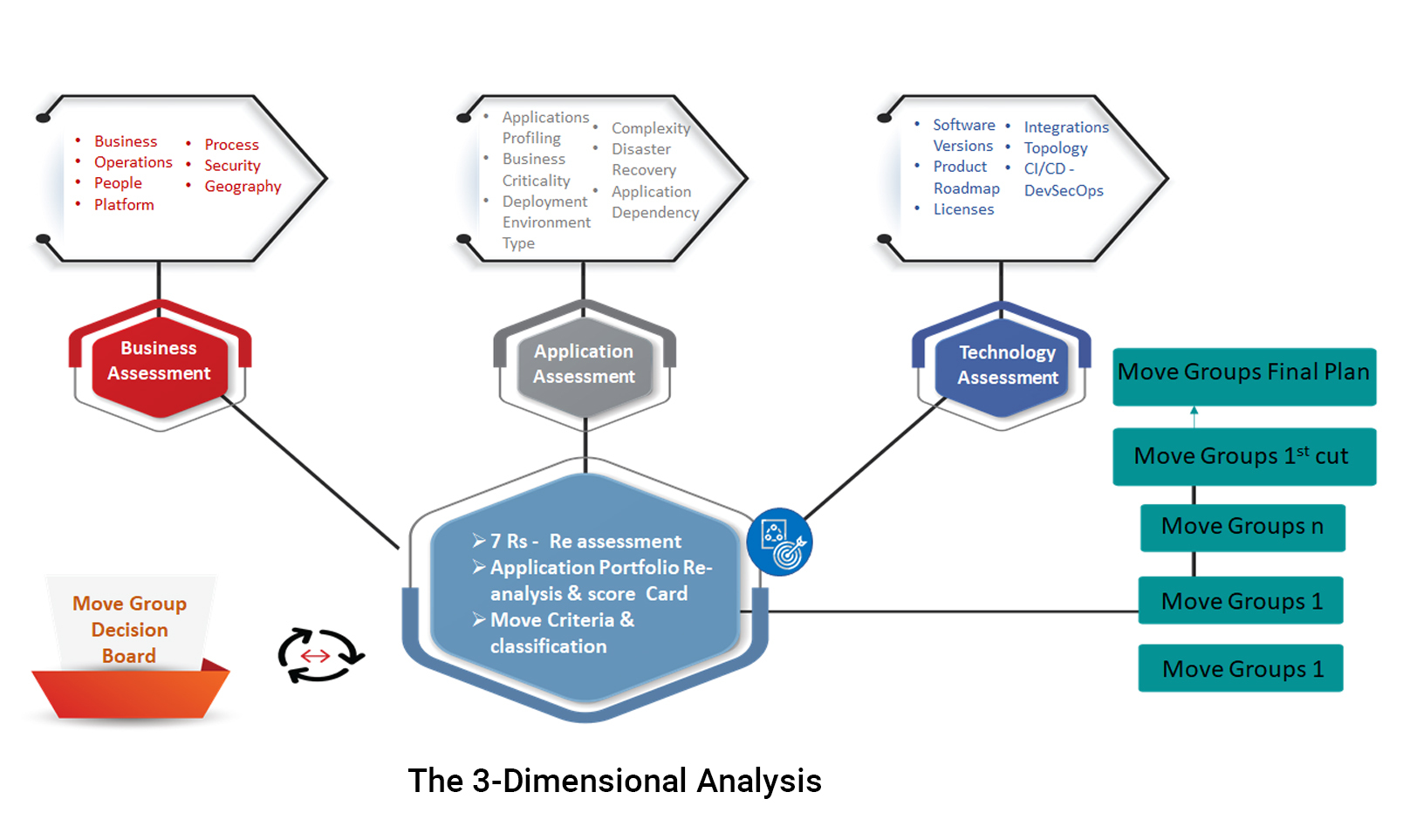
At this point, with the help of the 3-Dimensional Analysis, considerations for creating move groups (at quarterly release) such as the following are extended:
- Applications serving a specific business context (business function within a process) are moved together to reduce dependency on business, reduce risk to the program, and enable easy cutover/migration management.
- Applications with latency sensitive integrations will be moved together to prevent breaking of the latency requirements. This applies to applications with synchronous and semi-synchronous integrations, for which, additional latency caused by moving one application to cloud while the other remaining on-premises, is not acceptable.
- Technology specific lines within Application stream can handle the migration of applications belonging to certain category over a period. This, in turn, can ensure that the best practices and the lessons learnt are applied continuously in future migration.
- And, finally, a reassessment of the ‘7R’ models, and reanalysis of the application portfolio (with new score card) are also carried out for strategy accuracy calibration.
It is expected that some degree of arbitrary allocation of an application to one or other move groups may find some accommodation, where a clear allocation is not possible. It is expected that due to technical (e.g., latency) or functional issues, applications may have to be included in move group to which they do not clearly belong; or be excluded from their “natural” group. These types of issue are resolved during the Define phase and the subsequent detailed migration planning.
Hence, in short, all the segments under the Design phase including current state architecture, workload analysis, solution design, deployment design, migration design, architecture review/sizing, Move Groups, and the three-dimensional analysis, all collectively result in the finalization of the migration strategy and deliverables.
2.3. OCI Design – Virtual Cloud Network (VCN)
Virtual Cloud Network is the adequately the nervous system of both during, and after cloud migration is complete. However, having only a general-purpose VCN is not a fit for any migration strategy. Therefore, the following features should find place in a VCN, which the Oracle Cloud has built in.
Personalized VCN: Enterprises can define and divide VCNs using subnets, extend the existing networks (on-prem) via virtual routers/gateways and VPN Connect, and introduce reputed/whitelisted IPs against disruption or migration, and leverage FastConnect for directly connecting to VCN via private/dedicated connections. To render these features more valuable, Oracle also lets enterprises choose the port speed and accordingly pay a low, consistent price.
End-to-end security: The next essential feature-set in VCN is, naturally, the security. With isolated network virtualization (INV) via Oracle’s SmartNIC, Maximum Security Zones for custom security policy enforcement, Oracle Cloud Guard for monitoring and auto-remediation of events, and service gateways, etc., attacks on the network should be most seamlessly deterred, end-to-end.
Low-latency environment: This is indeed the most obvious requirement in a VCN, however, with Oracle VCN, it is a one step further. For example, the remote direct memory access (RDMA) via RoCE-v.2 can allow up to 100 Gbps, or the limited network hops (a.k.a. flat networking), gaining required low-latency and high performance is easy yet further secured with SLA.
High-priority workloads: Finally, VCN should have safeguarding measures in place for disaster, a web application firewall which is also PCI-compliant, and a multi-cloud compatibility.
2.4. The Unique Security-first Design of Oracle Cloud
Security-first design in Oracle Cloud is not merely an idea, or approach. Security in OCI physically begins at the foundational layer, i.e., the BIOS, and BMC firmware. With the usage of multiple storage chips like ROMs, BIOS/BMC SPI flash, DRAM, PCIe EPROMs like NICs, NVMe, etc; the famous off-box virtualization method; and by being the original device manufacturer (ODM) of all their motherboards, Oracle forms the securest base for any other cloud service provider to entirely follow.
Graduating to the next layers of services acquainted with the marvels of the 2nd generation Oracle Cloud—including:
- highly isolated logical tenancies, cross-tenant threat containment
- segregated hypervisor, and server/network virtualization
- the virtual cloud network (VCN)
- dynamic routing and service gateway (DRG, SG)
- availability and fault domains (AD, FD)
- network security groups
- subnets
- events and notifications
- automated threat remediation by Oracle Cloud Guard
- the default Zero-Trust, Always-on, and Maximum Security Zones enforcements
- Oracle Data Safe’s identity and access management (IAM), role-based access controls (RBAC), sensitive data discovery, masking, audit, and
- security and privacy compliance
—an impenetrable security posture is achieved for the enterprises.
This is further contributed by the enforcement of the industry-leading best practices, inclusive of power cycles, reinstallation of known-good firmware images, wiping and reinitiating of the Root-of-Trust hardware firmware including the critical mutable storage without compromising on the control they get from the very breed of the Oracle hardware.
Therefore, from the hardware, firmware, platforms, connectivity, operations, to data and applications – the OCI security features guarantee the unprecedented, round-the-clock security of enterprise assets and workloads against the ever-evolving threats including ransomwares, phishing, SQL injections, Eclypsium, etc.
A Quick Rundown on the Design Phase
- Infrastructure Design: The first segment of the Design phase concerns the target infrastructure, hence the target design, across the dimensions of security, foundation, and middleware for the platform. It also involves the finalization of application treatment and the identification of targets for PaaS cloud adoption models, followed by any modifications required thereof.
- Application Design: The next part in the list under the Design phase in cloud migration is the target design for enterprise applications, accompanied by database migration design.
- Migration Plan: The final segment consists of classification of the Move Groups, followed by establishing the testing plan, and the complete migration road map.
-
Deliver
It all boils down to the Deliver phase, in which, we implement the plan formulated in the Design phase with the Migration Factory approach via diverse tools and IPs based on Move Groups, further encapsulated in an incremental migration approach. The setup, in turn, effectively executes migration, integration, validation, and testing in parallel groups. However, most importantly, each segment in the Deliver phase goes through continuous evaluation and feedback loop, for learning and improving the overall process, and adding the last mile agility.
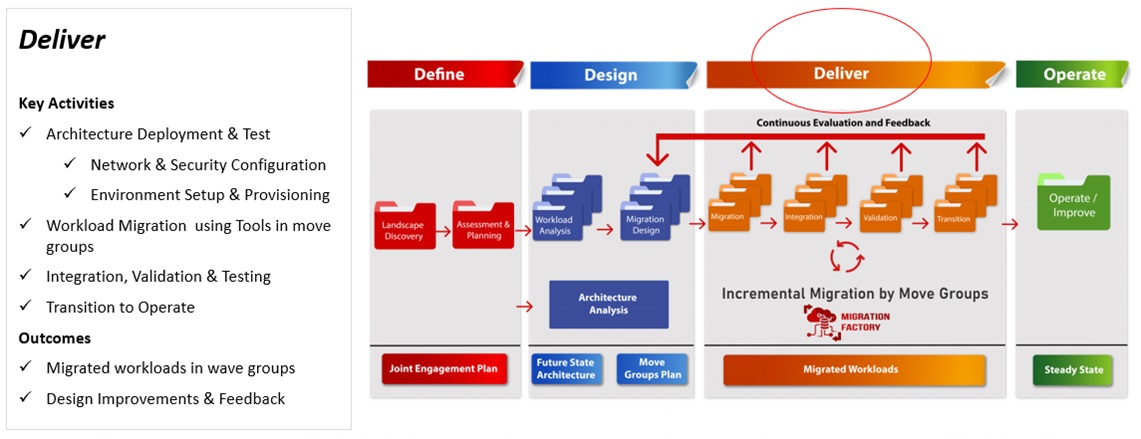
The Elements of the Phase Deliver
The Deliver phase has the architecture deployment and testing (including network/security configuration, environment setup, and provisioning), workload migration leveraging the Move Group tools, integration, validation, transition, and evolution. Owing to which, this phase is also known for the add-on design improvements, and wave groups.
Meanwhile, the iteration at the core is also significant because it enables artifacts to be more detailed and enter their greatly refined versions. The more times the iteration is executed, the more regular feedbacks and checks can ensure that the direction and hypothesis is correct and valid. For the otherwise cases, embracing early feedback loops ensures proactive course correction by the deployed team, as iterations help them learn more about the hypothesis, and if necessary, when to pivot or change the hypothesis.
Moreover, the principles underpinning the Enterprise Cloud Adoption Lifecycle (ECAL) have mainly come from the design thinking, lean startup, and agility, by avoiding long projects where the outcome is not known for extended periods of time. This leads to the required changes becoming very late, and sometimes impossible for implementation.
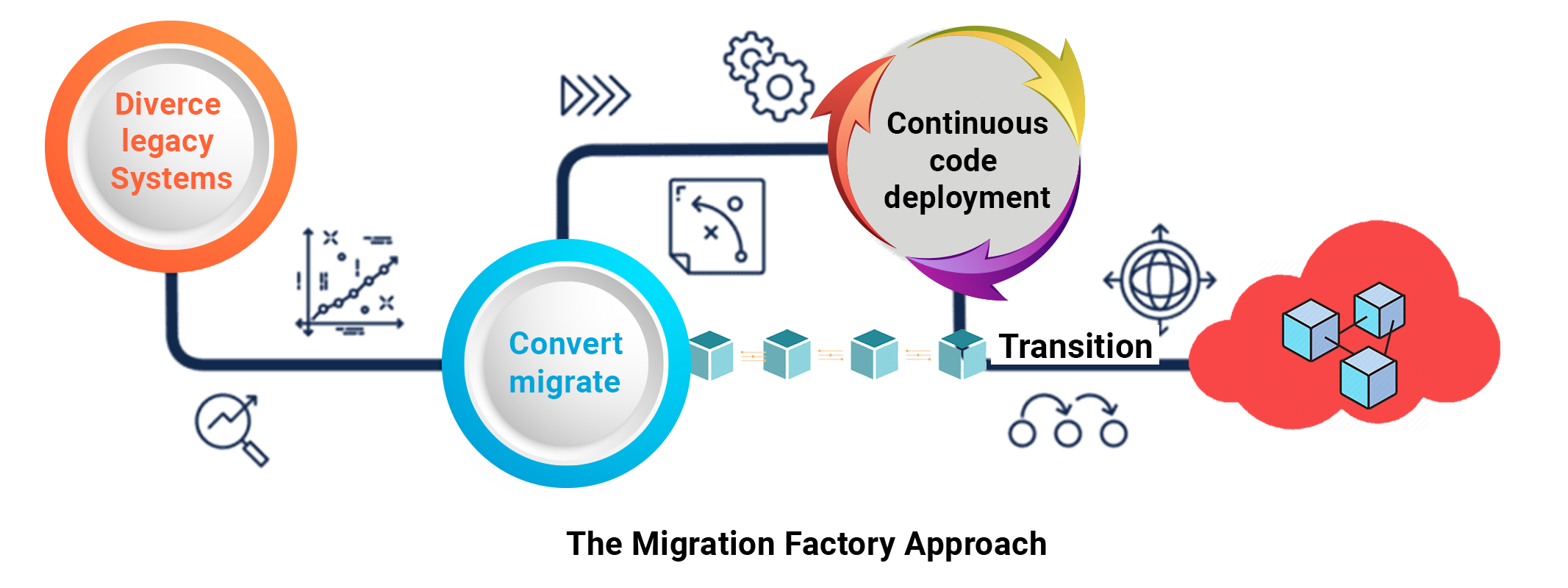
3.1. Migration Factory
The Problem
Enterprises have hundreds of legacy, custom, and independent software vendor (ISV) applications that critically need cloud migration for opening up the opportunities available to their competitors already on cloud. This includes leveraging the cloud-native capabilities such as the containers, the microservices architecture, development pipelines, serverless functions, infrastructure as a code, APIs, event-driven applications, the security, the performance, and the scalability – all while significantly reducing the costs of achieving the same functionalities on-premises.
However, migrating the mission-critical enterprise applications to the cloud demands minimum disruption, and accelerated time to market while also contemplating the concerns of the stakeholders, and abiding by the dynamic timelines.
Migration Factory Key Principles
To overcome these problems, the proven Migration Factory approach together with its pre-defined methods and accelerators require leveraging by the enterprises. And it starts with the efficient workflow for seamless pre- and post-migration tasks, followed by enabling automation and parallelism across processes, continuous improvements, review on the accuracy of executed tasks, and transparency by specialized teams comprehensively defining every step and the group of steps.
Benefits
By embracing the Migration Factory approach, enterprises enable a smarter, faster, better, and cheaper migration delivery at scale. Particularly, via expertise of the overall and specifics of the migration process, outcome focused Rate Card estimations, automation, parallelism, and standardization.
A Quick Rundown on the Deliver Phase
- Foundation Setup: Setting up of the domain controller (DC) for cloud or colocation comprise the first segment of tasks, followed by provisioning of the infrastructure, setting up of the middleware, network, and the configuration of the target environment encompassing user, access, security, and more.
- Migration and Integration: The next segment is about application remediation for cases that require it, followed by the changes in configuration in accordance with the design. This is then accompanied by the database migration, and the changes made within the infrastructure considering the target application design including security and firewall. Thereafter, the technical sanity of application on cloud/target platform is staged.
- Validation: The validation part of the Deliver phase is classified into three sections. In the first part, it involves the preparing of test requirements, defining of the test plans and implementation of automation. In the next section, it comprises the execution of the test in cloud and target DC, followed by testing the regression, performance, and the other non-functional requirements (NFRs) including reliability, maintainability, security, usability, scalability, etc. This is followed by the final section of tasks under Validation that comprise the reviewing, and signing-off, and furnishing of the test results.
- Cutover: Finally, the preparation of the rollout is initiated, i.e., switching from the source to the target. This involves creation of the migration runbook, followed by auditing and finalization. What also is the part of the cutover segment in the final phase of cloud migration is confirmation of operational readiness of the resources. The transition from KA to AMS teams is also duly verified for the final rollout to begin. The final step is the exercise migration from source to target and signing-off for the transformation to complete. From here on, the ‘business as usual’ (BAU) and the operate phase come into effect.
-
Operate – Infolob Cloud Managed Services
Upon the diligent implementation of all the above phases—and successful migration of the enterprise applications and workloads to the cloud—enterprises proceed to the Operate phase. It comprises the monitoring of asset functioning, proactive problem remediation, assurance of absolute security, performance management, cost management, regulatory compliance, and automation for all the cited assignments up to the most optimal extent. This also goes simultaneously with workforce training, change management, and metering consumption among others. To offer you a closer look:
Governance: Infolob Cloud Governance Services ensure global compliance of internal and external security and privacy regulations that includes acquainting you with the guidelines on compliance, usage, procurement, and management configuration of the database(s) – together with security, control, additional resource provisioning, and process standardization.
Change Management: Infolob Cloud Change Management Services facilitate initiation of change advisory board (CAB) guidelines, CI/CD frameworks, approval frameworks, and release management, followed by helping enterprises analyse CI/CD toolsets, define identity and access management (IAM), integrate ITIL change management, DevSecOps on-boarding, and patch management to discipline changes and deliver scalability and growth.
Automation: The aspect of automation in Infolob’s cloud managed services emphasizes on accomplishing consistency and repeatability of tasks, curtailing risks, and driving up productivity. Infolob also helps define a library of automated tasks that also encompass backup and disaster recovery. Just as Oracle, Infolob also welcomes open standards in identifying the automation opportunities in enterprise operations via third-party resources such as Terraform.
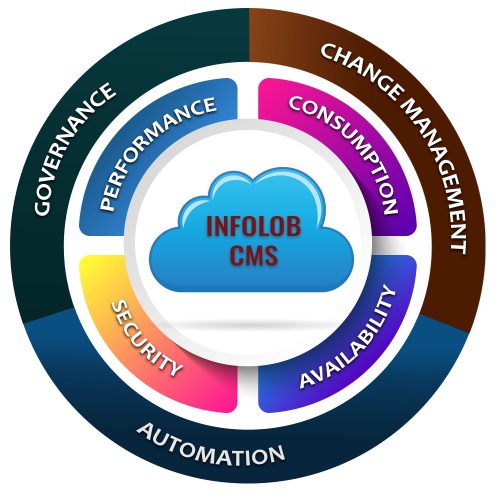
Elements in the Operate Phase – Infolob Cloud Managed Services
Performance: Infolob Cloud Performance Managed Services enable defining of business SLAs for performance and usage pattern monitoring, followed by the periodic auditing of service metrics, and production of heat maps to trace resource utilization tendencies, and dispensing of actionable recommendations and their implementation upon approval.
Security: Infolob Cloud Security Managed Services deal any internal/external threat by enforcing industry-leading security best practices that encompass users and their roles, the policies, the network security groups, etc. Infolob employs Oracle Cloud Guard and Oracle Data Safe for monitory security, while alerting enterprises of all anomalies, generating perimeter assessment reports on each security violation, and remediating OCI notifications.
Consumption: Infolob Cloud Cost Managed Services control cloud expenses via setting procurement guidelines, observing daily cost variations, trailing resource utilization, and raising alarms on violations pertaining to cost threshold exceed and provisioning. Together with the adequate implementation of latest resources and capability updates from Oracle, Infolob helps reduce the cost and the intricacies of IT and cloud resource management.
Wrapping up Operate Phase and Cloud Migration
The criticality of the Operate phase can be measured by the fact that, irrespective of the success in the previous phases, the Operate phase alone ensures the continuous returns on investment. Having said that – all four phases are the pillars of true business transformation that does not only help enterprises most conveniently run their mission-critical workloads using the latest technology, however, also change the way businesses—together with the workflows, value and supply chain, management, and IT—dynamically operate in an environment that demands it.
With Infolob, businesses save 30% – 50% on the training and operating costs of in-house cloud management teams, while also regain focus on innovation and continuous delivery of their products that directly impact their growth. Infolob’s time-tested cloud migration and managed services in conjunction with our scientific methodology for successful cloud migration leverage the expertise, advanced proprietary and open-standard utilities, the OCI, and industry best practices to help enterprises upgrade and optimally run their IT environments in the 2nd generation cloud.